The CFO Question That Changed the Conversation
Health plan CFOs used to evaluate risk adjustment programs on a simple formula: investment in chart review versus revenue recovered. The ROI calculation was straightforward. Spend X on coding. Recover Y in higher capitation payments. As long as Y exceeded X by a comfortable margin, the program was working.
That formula is broken. Revenue recovered is no longer the right numerator, because revenue that gets clawed back in a RADV audit or surrendered in a DOJ settlement isn’t revenue. It’s deferred liability. The Aetna settlement cost $117.7 million. Kaiser paid $556 million. OIG audits routinely estimate millions in overpayments from just two payment years. When the CFO calculates ROI, the denominator now has to include the probability-weighted cost of enforcement outcomes.
The question CFOs should be asking isn’t “how much revenue does our risk adjustment program generate?” It’s “how much of what we’ve submitted can we actually defend?” That question changes everything about how the program is structured, what technology supports it, and how success is measured.
Why Defensibility Is a Financial Metric
Every submitted HCC code sits on the plan’s balance sheet as either an asset or a contingent liability. If the code is supported by encounter-linked documentation, validated against MEAT criteria, and backed by an explainable evidence trail, it’s an asset. If it’s not, it’s a liability that materializes when CMS audits it, when OIG investigates it, or when a whistleblower reports it.
CFOs need visibility into which category their submitted codes fall into. That requires technology that scores defensibility at the code level, the member level, and the population level. How many of your submitted HCCs have strong MEAT evidence? How many have marginal evidence? How many have no current documentation support? The answers to those questions determine your real financial position, not just your reported RAF scores.
Plans that can’t answer these questions are carrying unquantified risk on their books. Credit agencies have already started flagging MA profitability risk tied to risk adjustment changes. Investors are asking harder questions about revenue sustainability. A CFO who can demonstrate that 95% of submitted codes are audit-defensible has a fundamentally different conversation with the board than one who can only report total revenue captured.
What a Defensibility-First Architecture Looks Like
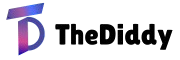
The technology shift is from revenue-first to defensibility-first. In a revenue-first system, the primary output is codes identified and submitted. Validation is a secondary check. In a defensibility-first system, the primary output is an evidence-validated coding package where every HCC is linked to specific clinical documentation, specific MEAT elements, and explainable AI reasoning. Revenue is the downstream result of accurate, defensible coding.
This requires a platform that handles the full workflow: chart retrieval, AI-assisted MEAT validation, two-way coding (adds and deletes), quality assurance, audit simulation, and RADV response management. When these functions operate in a single environment, the evidence trail is continuous. The CFO gets real-time visibility into defensibility scores. The compliance team can audit AI decisions. The audit response team can generate submission packages without manual assembly.
Fragmented systems that spread these functions across multiple vendors and platforms can’t produce defensibility metrics at scale. The data reconciliation required to assemble a cross-system view of coding quality is manual, error-prone, and too slow for the audit timelines CMS now enforces.
The Financial Case for Platform Investment
The cost of a unified Risk Adjustment Platform is measurable. The cost of not having one is also measurable, but the numbers are larger: settlement payments, recoupment demands, audit remediation expenses, legal fees, and the opportunity cost of executive attention diverted to enforcement response. CFOs who compare platform investment against settlement risk, rather than against the cost of maintaining fragmented systems, will find the math strongly favors consolidation. The plans that make this investment now are building the financial infrastructure that the enforcement environment demands.